
December 2019
SCIF Life
There's a whole lot going on in the news, and the way society has become tribal it is best not to mix politics at work. But meet up with me anytime and I'll tell you how I really feel.
On politically neutral ground, the topic of SCIFs (Sensitive Compartmented Information Facilities) has been in the news for a couple of reasons: A phone call record from the White House that should have been a routine call log was placed on a "top secret server" to limit access to it. That type of server is usually in a SCIF. During a closed session of the House Intelligence committee, Republican representives stormed a SCIF, carrying cell phones. That is a huge breach of SCIF protocol, and if you did it at work you would be fired instantly and you would be visited by some government people who would be interested in what you thought you were doing. Why is it so bad to bring a cell phone into a SCIF? Because a mobile phone can easily be hacked to become an audio or video source for adversaries.,
Let's talk about security and SCIFs. Millions of people work in them every day. There ought to be a web site, magazine or blog titled "SCIF Life" with that many people involved, maybe this will be the start of something huge.
The good news for me is that I don't need to post any images, as it is theoretically impossible to take a picture inside a SCIF. Unless you are part of the Party of Law and Order.
Note to readers: it is OK to talk about how SCIFs operate, but it is not OK to talk about what happens inside them.
FSO
The facility security officer (FSO) is in charge of ensuring that government rules and regulations are obeyed in a SCIF. When in doubt, talk to them. They are there to help you, but when something bad happens, they will be on the side of the government. If you are careless and spill data, they are not going to help you hide your infractions, unless you are "Individual 1".
Clearance
There are hierarchical government classifications for security clearances, starting with Confidential, then Secret, then Top Secret. Not all government entities recognize each other's clearance levels, an added complication. If you don't have Secret, your only chance of seeing inside a SCIF is joining maintenance so you can change the lightbulbs while the FSO holds the ladder.
SF-86
The first step to obtaining a government clearance is being asked to fill out the SF-86 form, which is currently 136 pages in a pdf form document. SF-86 includes your social security number, your criminal record, information on family members, neighbors, passport and citizenship, and instances of psychiatric evaluation. Stuff that you'd rather not share with anyone, but hey, be a patriot and fill it out. Here's a copy of the form:
https://www.opm.gov/forms/pdf_fill/sf86.pdf
The form asks about drug use. I would like to see a study on how many people lie about smoking weed.
E-QIP website
The E-QIP website (Electronic Questionnaires for Investigations Processing) is the portal for filling out the SF-86 and submitting it. It is currently located here:
https://nbib.opm.gov/e-qip-background-investigations/
You can imagine how well-designed a governent web site might be. In 2015, E-QIP was massively hacked, and 21.5 million people with clearances had data stolen. China is the lead suspect.
https://www.nbcnews.com/tech/security/opm-hack-security-breach-n389476
Shortly thereafter, the goverment set up a site so you could verify if you were hacked:
https://www.nextgov.com/cybersecurity/2015/11/new-pentagon-website-tells-anyone-if-theyve-been-hacked-china/123915/
As a booby prize for losing all your data, the government offers free identity monitoring, and there is a current debate on whether to extend it for the lifetime of those affected. This will cost the Government $1B eventually. The way things are run today, that check is probably being written to someone's brother-in-law or a campaign donor.
I met an ex-three-letter-agency guy once and asked him about whether signing up for identity monitoring was a good idea. His answer was it was just one more way to get hacked, don't do it. The best thing you can do is to change your password regularly.
The ownership of personnel records was moved to DOD on Sept 27 this year, by White House Executive Order 13869. It was previously administered by Office of Personnal Management. Someday I hope to hear the back story about why this huge disruption was necessary.
https://nbib.opm.gov/news/nbib-news/2019/09/nbib-website-content-moving-to-dcsa-on-september-27/
The interview
Your SF-86 gets submitted to the government, and is reviewed, then someone you have never met calls you and sets up an interview. They will show you a badge just like on crime dramas. Ask them for a business card to impress your friends. They have access to your SF-86 and much more, including credit reports, and interviews with your neighbors, and maybe a peek in your recycle bin to count the brown liquor bottles. They will ask questions, focusing on all the questionable things from your background, such as that time you forgot to pay your mortgage and the bank downgraded your credit rating. Be sure to double down on anti-perspirant.
Polygraph
In some cases you will need to do a polygraph. As far as I can tell, no one has ever said "that polygraph was such a good time!" Perhaps someone said "that was better than being waterboarded". There are rules and regulations on polygraph testing, you should read them before you submit to one. For example
Questions probing a person’s religious, racial, or political beliefs and lawful affiliations that are not related directly to the investigation are prohibited.
Note that it didn't say that they can't ask if you are cheating on your wife... You can find more info on government polygraph regulations by Googling. Here is an example document:
https://www.esd.whs.mil/Portals/54/Documents/DD/issuances/dodi/521091p.pdf?ver=2019-04-22-104603-167
You have to wonder why engineers are subjected to polygraphing, but you never hear about anyone forced into it in a Congressional investigation.
SAP programs
Programs that are compartmented are called special access programs (SAP), these are what need to reside in a SCIF. One big difference between DOD Secret and SAP materials is that for access to Secret material, all you need is the proper clearance and a need-to-know. That need-to-know can be a judgment call from a co-worker or manager. On a SAP program, you need a special invitation from a customer that probably does not want to be indentified. Top Secret clearance is not necessarily needed for an invite to a SAP program, but it is desirable and may help the invitee get clearance faster. Some SAP programs require TS clearance.
Using multiple SCIFs (and programs) allows the company (and government) to stovepipe various projects and only allow key people (systems designers, tech directors, managers) to know the big picture. If you don't know what is going on, chances are the nation's adversaries are having trouble putting the pieces together. This technique dates back to WWII, at least. Navajo Indian tribe mining uranium in Arizona? I have no idea why... but rest assured, if the Government asked them to do it, it must be safe!
Your nomination
Somewhere in the bowels of your company or service branch, a special access program (SAP) decides they need your expertise and they nominate you for access. Soon after, you may be asked to update your SF-86, even though your normal clearance does not expire for a few more years. You fill it in again (always keep a paper copy of it so your data are consistent). Your data will be brought inside the program and shared with the program's sponsor, the government agency that is paying for it. They get to decide if you can be trusted or not. It is illegal for your company people to adjudicate your status, or even talk about it. If your SF86 includes an arrest record and you hear people snickering about it later, you have a good basis for legal action.
Things that matter most in a SAP program are foreign contacts, foreign travel and foreign relatives. I hate to say this, but if you are married tio a spouse that has relatives that he/she keeps in touch with in China, you might save yourself the trouble of applying.
What is a SCIF?
A SCIF is designed to prevent data from leaking. It must be built securely, kept locked up, and the information processing system inside (computers, servers) must be disconnected from the world-wide web. Data can be brought in, typically on DVDs, these must be scanned for viruses before the information is copied to the server. Inside the SCIF the DVD is destroyed. You can put it inside a microwave for three seconds and cook the data, for example
The SCIF is typically part of a secure area that starts with a locked door that requires an idividual PIN code to access. No tailgating is allowed. Entering the secure area, if times are good, a full time receptionist will welcome you and check your badge to see if you have access. There could be a special code on your company badge, or there may be a special badge for the secure area. The special program badges may be attached to a wall rack.
A cell phone locker will be available, you need to lock up your phone. Perhaps the receptionist does that for you, and gives you a token or a key to retreive it later. In some areas, there may be a special receiver that monitors cell phones to make sure they are turned off. It is possible to use a one-way pager in a SCIF, which seems old school but it is helpful in case someone is looking for you.
If this is your first time, a security person will accompany you to the SCIF where you will work and admit you, the door lock will have a five button combination with an eye shield around it. Whoever brought you in will say loudly "uncleared" so that people stop any classified work. Sometimes they might say "unclean", as a reference to leperosy, it's just a tragic example of enginering humor. You will see a flashing light (indicating someone is uncleared) when you come in, and then see some co-workers you may or may not recognize. Then the security person will read you onto the program, you will sign a document, and the light will be turned off. Congratulations are not really in order, this process opens the door to a project that can take away a significant part of your life.
As part of the indoctrination you will learn the program's nickname, which is usually then abbreviated into three letters. These three letters are used in marking all documents that are generated
You will be fixed up with a special login for the secure computer or server.
Communicating outside the SCIF
How do you communicate with the program sponsor, if no connections to the web are allowed? There at least four ways:
- You can mail media (paper or electronic) if you follow some specific rules. Typically the program's FSO will take care of this
- You can visit their SCIF, or they can visit you. Just be sure NOT to say anything that is program sensitive to make conversation when you are standing at adjacent urinals
- You can use a STE phone.
- In very high-end cases, a secure network is possible through encrypted transmission. However, the bandwidth is restricted to Morse-code like data rates, so don't plan on sharing 3D models.
The video below make STE look like a great thing. It's not. It takes a while to set up a call. Your call starts out as unsecure, then one of you pushes a button, you wait and see if the secure lite goes on. Once it is secure, everyone sounds like Donald Duck. This is probably why no STE phopne manufacturer posts secure audio examples on Youtube.
Wow, caller ID.
That whole "pushing the button" thing reminds me of someone that used to sit over the wall from me. Every day he would call his wife and talk for 30 minutes. When it was time to go back to work, they would go through this ritual of "you hang up first"... "no you hang up first". Super-annoying 50-something-second-marrage-lovebirds. Little did they know, they are part of a meme
Did you just hang up on me?
OPSEC (operation security)
Part of being read onto the program may be providing a story to help you deflect questions about what you are doing. One generic description that is often used is "it's a proprietary program", which is never a huge stretch of the truth. You should let the FSO know if it bothers you to tell a white lie or two, even though it might cost you your ticket to the secure job. Money talks, and people of all religions and beliefs work on secure programs every day. Obviously, it is best to just never talk about what you do, which many people will find difficult. You need to keep a tight lid on your activities. As various bits of information slip out, uncleared people might start guessing about what is going on in the company during lunch break. Just walk away and eat some Tums. If people persist in asking you about your job, part of your training will involve finking them out to security. You might lose a friend, but it's all worth it!
You may encounter times when your CEO seems to be blabbing about the work that is going on. You can rest assured that your leadership was granted permission to reveal just enough to impress Wall Street.
https://boingboing.net/2019/11/29/your-tax-dollars-at-work.html
The cover story for Adu Graib torture (a SAP program from Hell) was "some kids got out of control". In that case, investigative journalism got to the truth of the matter. Hopefully your "proprietary" project does not involve war crimes, and the Washington Post won't be bugging you.
https://books.google.com/books?id=DQ-gCwAAQBAJ&pg=PA2008-IA13&lpg=PA2008-IA13&dq=sap+program+cover+story&source=bl&ots=c4ZcQd2Eml&sig=ACfU3U2JUT5ckQtaY7kgzVenEneN-N_ZXg&hl=en&sa=X&ved=2ahUKEwiHtsiOm6LmAhVBCjQIHYi_ANkQ6AEwA3oECAoQAQ#v=onepage&q=sap%20program%20cover%20story&f=false
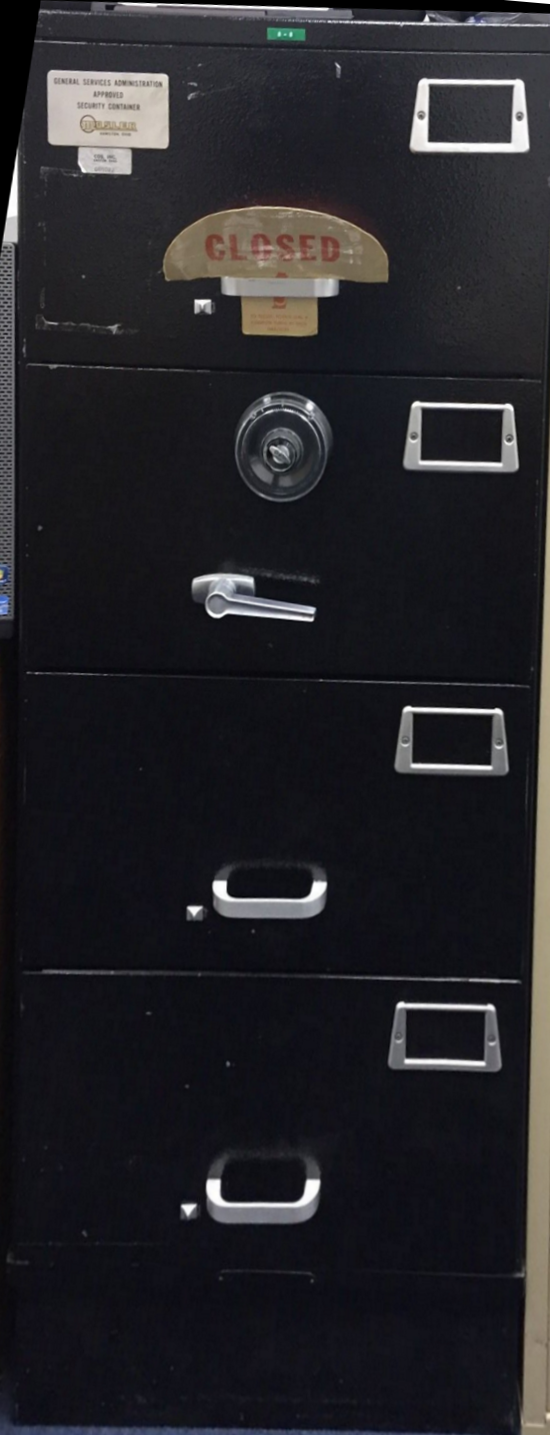
Safes and door locks
You will see a Mosler safe in the SCIF, it is used to store documents as well as the hard drives from the computers. Mosler was a US company that filed bankrupty in 2001 but the word Mosler has the same status in the world of safes as "Xerox" does to copiers. The four-drawer safe in your SCIF can weigh up to 600 lbs. (272 kg), they don't want to make it easy to move. After some time on the program you might get closing privileges, and then you will learn how to lock up everything and turn on the alarm. Later when you get opening privileges, pay attention to how to disarm the alarm, or you will immediately get a very serious visitor to ask some very uncomfortable questions.
Because security personel have to keep track of dozens of combiations, a memory trick can be used. For this you will need to memorize the numbers and letters on a phone, or perhaps keep an image of a phone handy (not your actual cell phone!)
|
1=no code
2=A,B or C
3=D,Eor F
4=G,H, or I
5= J, K or L
6=M, N or O
7=P, Q, R or S
8=T, U or V
9=W, X, Y, Z
0= no code
|
 |
Then think of a six letter word and convert it to numbers. For example: felony. Felony translates to 3,3,5,6,6,9. Now group the numbers into two-digit numbers and you get 22, 56, and 69, this satisfies the need for three two-digit numbers on a spin lock. In many cases you will need to have those numbers in mind, pulled up and ready to go (not sitting there thinking about the phone code) as many locks have time-out features. In any case it is far easier to remember "felony" than 22, 56, 69. You probably won't be involved in picking the code--someone will just whisper it to you if you need it-- but you can still try the memory trick backwards by converting the numbers you're given to letters and seeing if you can get a word out of them. You can expect the code to change every time someone is read off a program, retires or takes another job.
Way back when, telephone exchanges used the same trick. I used to live in Deerfield-4 (334), in Towaco, New Jersey.
In case you were wondering how it is done, here is a MIL-Spec document on how to change the combincation of a Mosler safe. Paragraph 2.1.3 provides some rules on picking combinations you will need to follow. If you screw up resetting a safe cmbination, all hope is not lost. You call a locksmith and he/she drills out the lock. Scrap steel currently sells for $20/ton.
Obviously, you are never to write down a combination or password. Years ago, I knew someone who had suffered a stroke and had limited memory, and carried the code in his wallet. Everyone looked the other way when he pulled it out. The statute of limitations probably applies to his crimes by now, if he is still alive. If you ask me who it was, my answer is "I don't remember". That answer was used repeatedly in the Mueller Report.
Marking documents
This is not largely different from marking normal DOD classified documents: in all documents inside the SCIF, you will have to mark every paragraph at a classification level. This may drive you nuts, and possibly infect how you write outside. Your Christmas letter could look like:
(U) Greetings from Tucson, it's been a fantastic year! Steve got promoted to CEO, the kids are finishing their law degrees, and Brenda's novel was optioned for a movie!
That (U) refers to the information being unclassified. Other paragraphs might be marked (S/xxx) for secret, where xxx is the Code Word That Can Never Be Said Outside. If the program code word was "FEEBLE" the three-letter code might be FBL. It is unlikely that the military would label any program "feeble" or "waste" or "crazy", more likely "grandious" or "spectacular". If the paragraph contains the nickname but is otherwise unclassified, it will have to be labeled (HVSACO) which means handle via special access only. This term is pronouced "have sake oh".
You can learn more about SAP protocols in "DoD Special Access Program (SAP) Security Manual: General Procedures"
SCIF life
Here's the new normal. You get to work, screw off at your cube for a bit, then head for the secure facility with a bathroom stop on the way. Then you go inside and work on some stuff that you can't talk about. You don't see the sun until lunch time. If it is crunch time, someone will bring in some cheap pizza or Taco Bell for you. The SCIF has various requirements on the air vents, which are not conducive to fresh air, so you will be smelling that double-Whopper you discard in the unclassified trash bin long enough so you don't notice it. But that smell will come back to you tomorrow, so be sure to put the trash bins in the hall way.
Even though the secret server is not connected to the world wide web, SCIFs often allow a non-secure computer termninal inside so you can check email and do whatever you do when you think no one is looking. There is some wieird rule about how it has to be three feet from any classified gear. Modern companies have net-nanny capabilities, you can be assured they will be monitoring you, specially in the SCIF. If you want to test this out, just try to visit the wikileaks web site. That was sarcasm.... please, don't even try to do that from home!
An old-school desk phone (non-secure) should be provided inside the SCIF. It's been a while since you used one, right? Did you ever look at all the ear crud on the handset? You might find some cleaning products nearby for this purpose.
The SCIF of course will include a coffee setup, we would not want you to fall asleep. However, a SCIF never includes a bathroom, you will be at least two locked doors from the plumbing, and if you are alone, you will have to arm the alarm to pee. Rumor has it that in some SCIFs there may be gallon jugs under the table...
Security violations
This is one of the downsides of working in a SAP program. Suppose you forgot to remove your cell phone when you entered... if it rings you are in for bad times. The first instance will require "training" and begging for forgiveness. The second offense will likely up the begging to government level. The third offense is probably going to cost you some time off without pay. Aren't you glad you work in a SCIF? Other security violations include forgetting to arm the alarm, leaving the safe open, leaving classified documents or hard drives out when the SCIF is closed up. You might even get yelled at for not initializing the log book that says you opened or closed the facility.
If you do everything right and never get a security violation, don't think you deserve any reward. Millions of people do work in SCIFs everyday and do thier best to obey the rules. One thing that would improve morale would be if the leadership of our country obeyed the rules too.
Of course, I don't know anything about this topic first hand.
Check out the Unknown Editor's amazing archives when you are looking for a way to screw off for a couple of hours or more!
Fan/hate mail can always be sent to UE@microwaves101.com